Securing MS 365 users in an unsafe environment. Why 2FA alone is not enough and how to strengthen protection with IAM and Microsoft Defender
In the age of digital transformation, remote working and cloud services, the need to protect data and users is growing by the day. Microsoft 365, as one of the most widely used remote working environments, is vulnerable to a variety of threats, from phishing to malware attacks. While the inclusion of two-factor authentication (2FA) is an important step toward security, 2FA alone does not provide full protection. This article shows how you can do more by strengthening user protection with identity identity solutions (IAM) and tools such as Microsoft Defender.
Two-factor authentication is a key component of modern security systems, as it requires users to confirm their identity with two independent components, such as a password and a code from an authentication application. This ensures that even if the password is intercepted by an attacker, without the additional code access to the account is impossible.
1. two-factor authentication (2FA) – why is it only the first step?
However, 2FA alone does not provide full protection. Here are the main reasons:
- Vulnerability to phishing: Some forms of 2FA, such as SMS, can be vulnerable to interception by attackers.
- Loss of authentication device: If a phone or device with an authentication app is lost, users may have trouble accessing their accounts.
- Security limitations with weak passwords: 2FA does not protect against the use of simple, easy-to-guess passwords that may be vulnerable to brute-force attacks.
While implementing 2FA is a key part of protecting users, companies should go a step further and consider a full identity management (IAM) approach and the use of advanced tools such as Microsoft Defender.
2. extend user security with Identity and Access Management (IAM)
Identity and Access Management (IAM) is a comprehensive set of tools and strategies that allows companies to manage user identities and access to resources at a much more advanced level than traditional 2FA. Here’s how IAM can enhance security:
a. Strong password rules and enforcing them
One of the key elements of IAM is enforcing strong passwords. Although passwords can be vulnerable to interception, strong passwords minimize the risk of cracking them. IAM systems allow companies to set rules on the minimum length of passwords, their complexity and how often they should be changed.
Implementation Tips:
- Set policies for the minimum number of characters (e.g., at least 12 characters).
- Enforce the need for capital letters, numbers and special characters.
- Limit the reuse of passwords and implement a policy of changing them regularly (e.g., every 90 days).
b. Login blocking after unsuccessful authorization attempts
The IAM system allows you to set an account lockout after several failed login attempts. This type of security prevents brute-force attacks, which involve trying to guess passwords.
Implementation Tips:
- Configure account lockout after 5-10 failed login attempts.
- Set a temporary lock so that the user can only try again after a certain period of time or require manual unlocking by an administrator.
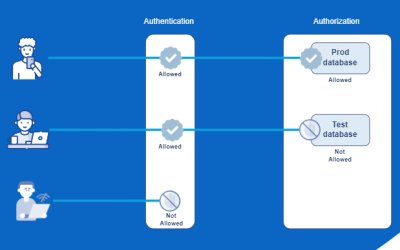
c. Role-Based Access Control (RBAC).
With IAM, you can control who has access to what in your Microsoft 365 environment. By assigning users roles with minimal access, you limit the number of people who have full administrative privileges.
Implementation Tips:
- Create user groups based on their roles and assign them only the necessary permissions.
- Regularly review and update user roles to meet current business needs.
3. Microsoft Defender: advanced threat protection
Microsoft Defender offers a wide range of tools to protect your Microsoft 365 environment from a variety of threats, such as phishing attacks, malware and ransomware. When combined with IAM, Defender creates a protection system that minimizes risk and protects users at every stage.
a. Microsoft Defender for Office 365: Mail and file threat detection
Microsoft Defender for Office 365 offers advanced features to protect mail and data stored in a cloud environment:
- Scans emails and attachments for malware.
- Detecting phishing threats and notifying users of suspicious messages.
- Blocking access to infected files and isolating them, which protects the entire environment.
Implementation Tips:
- Configure email filtering rules to block suspicious domains and senders.
- Enable warnings to users about the potential dangers of clicking on links or downloading attachments.
b. Microsoft Defender for Endpoint: Device protection and threat analysis.
Microsoft Defender for Endpoint is an endpoint protection tool that allows monitoring and analyzing user behavior at the device level. This is crucial because attacks can come from both the user and device levels.
Implementation Tips:
- Configure Defender for Endpoint on all corporate devices to enable threat detection and response.
- Regularly analyze incident reports to identify and neutralize potential threats.
c. Microsoft Defender for Identity: monitoring and analysis of user activities.
Defender for Identity allows companies to monitor abnormal user behavior and detect potential threats, such as attempts to access resources without proper privileges or actions that could indicate an internal attack.
Implementation Tips:
- Set up notifications for unusual user activities, such as logins from unusual locations.
- Use user behavior analysis tools to detect potential insider threats.
4. integration of IAM and Microsoft Defender: a comprehensive approach to security
The combination of IAM and Microsoft Defender enables a full, multi-level security system in a Microsoft 365 environment. This approach allows the company to comprehensively secure users, protect data and control access, minimizing the risk of both internal and external threats.
Example implementation steps:
- Automate privilege assignment in IAM: Define privilege assignment rules that automatically assign access to users based on their role and location.
- Enable threat monitoring at the device and identity level: Use Defender and IAM reports to monitor abnormal activity and take quick steps in case of incidents.
- Create backups and secure critical resources: Regular backups and the creation of critical data access policies will allow you to quickly recover data and restore normal operations in the event of incidents.
Summary
User and data security in a Microsoft 365 environment requires an approach that goes beyond just 2FA. Implementing IAM and advanced Microsoft Defender tools creates a complete protection strategy that not only protects against the most common threats, but also enables ongoing analysis and rapid incident response.
The implementation of these solutions can be carried out on your own, but given the complexity of the entire process, you should consider enlisting the help of professional companies specializing in cyber security, such as jeton.pl. Such entities can not only carry out the full configuration of security systems, but also advise on the further development of security policies tailored to the specifics of your organization.
Keep in mind that proper implementation of security features is not only a matter of tools, but also of experienced professionals who can use them to their full potential.